Home
Creates easy-to-understand organization and visualization of past project documents as basis for current projects
Challenges on Security Design

I'm worried if my design is secure ...
I don't know the best practices for this system ...
Entrusting everything to an expert costs too much time and money ...
I don't know the best practices for this system ...
Entrusting everything to an expert costs too much time and money ...
With SecureRAG for Safe Data Utilization
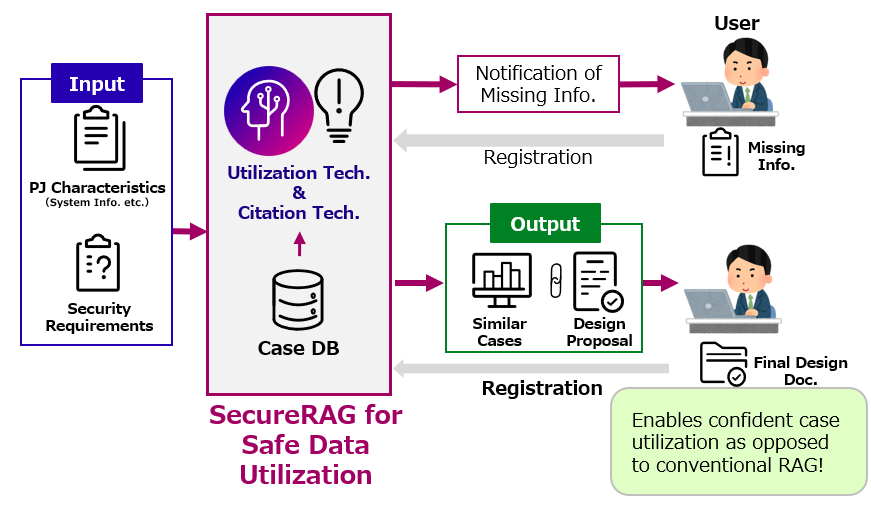
This allows for the easy generation, via generative AI, of highly explanatory design drafts, including points for consideration, for the security design of systems under development, based on past project design (track record/achievements).
This enables you to explain "why this design was chosen" based on past results, thereby increasing your confidence in your own judgment.
Furthermore, expert reviews are based on a draft rather than starting from scratch, which can reduce costs and shorten lead times.
This enables you to explain "why this design was chosen" based on past results, thereby increasing your confidence in your own judgment.
Furthermore, expert reviews are based on a draft rather than starting from scratch, which can reduce costs and shorten lead times.
Technical Overview
Target Industry/Users
IT department personnel at companies, system developers.
Technical Challenges
Ideally, you want to register multiple past project documents as RAG†1 and identify cases similar to your current project†2 for fast reference. However:
- Conventional AI provides insufficient explanations of why cases are considered similar, making human validation difficult.
- Generative AI may hallucinate citations not found in original sources, requiring manual verification and correction.
†1 RAG: Retrieval-Augmented Generation
†2 Projects assume security design for system development and operation; “similar” cases refer to projects with similar conditions such as OS and middleware.
The benefits of SecureRAG for Safe Data Utilization
- Users can select similar projects
- Similar past cases are visualized and grouped, enabling users to select the most valuable reference projects.
- For example, when designing system security, previously implemented security measures can be readily referenced.
- Ensures accurate citations from references
- Automatically detects and corrects generative AI citations not found in past cases or references.
- Improves the reliability of LLM-generated proposals, reducing the need for manual validation and correction.
Fujitsu's Technological Advantage
- Utilization Technology
A new similarity representation based on hierarchical classification for intuitive case grouping. - Citation Technology
Selectively applies “Fast Correction” or “LLM†3 Self-Correction” depending on the degree of hallucination. This is achieved without LLM dependency and achieves a world‑best score in sentence‑level citation benchmarks†4.
†3 LLM: Large Language Model
†4 As of June 23, 2025 (Benchmark:LongBench-Cite)
Use Cases
- Security Measures at the Design Stage
Implement necessary security measures during the system development design phase, referencing other projects.
Case Studies
- Case Study: System Logging Design
Based on sample project design documents and NIST CSF compliance, we will visualize and propose security countermeasures for detailed system log output and storage designs, accounting for OS-specific variations.
Related Information
- For Corporate Trials
If you wish to try the service, please contact us via the inquiry form and include "Request for trial of SecureRAG for Safe Data Utilization" in your message.
